Expert Warns of North Korea's Growing Cyberwar Capabilities
VOA
15 Oct 2017, 08:35 GMT+10

Thirteen months ago, South Korea's defense intranet was hacked for the first time, and the military accused North Korea of infecting hundreds, possibly thousands of computers with malware.
In December 2016, Han Min-koo, then defense minister, told lawmakers that the incident was not critical.
Now, the latest reports suggest that North Korean hackers might have acquired the so-called Operation Plan 5015 during the September 2016 cyberattack.
Oplan 5015, which, according to news reports, includes plans for the 'decapitation' of North Korea's leadership, is the key military operational blueprint drawn up by Washington and Seoul on how to react in the event of a North Korean invasion.
Pentagon officials have declined to comment on whether sensitive or secret information was leaked as a result of the hacking.
Kenneth Geers, a NATO Cooperative Cyber Defense Center of Excellence ambassador and a senior fellow at the Atlantic Council's Cyber Statecraft Initiative, told VOA's Korean service it was 'entirely possible' that these plans had been hacked and that North Korea might have received help from Russia or China in obtaining them.
Geers also said that Moscow and Beijing seemed to be closely aligned with Pyongyang on cyberwarfare, as they want to go beyond testing the traditional U.S. military and assess its cyberwar capability.
Geers' 20 years of experience in the U.S. government includes time in the U.S. Army, at the National Security Agency and at the U.S. Naval Criminal Investigative Service. He has also worked as a senior global threat analyst at FireEye, a California cybersecurity company.
Geers discussed the latest developments in North Korea's cyberwarfare capabilities with VOA earlier this week. His remarks have been edited for clarity and length:
VOA: South Korean lawmaker Lee Cheol-hee, a member of the ruling Democratic Party and a member of the parliamentary national defense committee, said that North Korean hackers stole the U.S. and South Korean war plan, Operation Plan 5015. Does the North have the capacity to do this?
Kenneth Geers: I think that once you digitize information it is very hard to hang on to it. That is true for everyone. The number of people who might have had access to these war plans and secrets is not low hellip; so that increases the odds [they will get out]. Basically internet usage of cyberspace has made this a golden era for espionage. You can relatively easily hack into systems large enough to have multiple vulnerabilities and [find] timely information. North Koreans know well who in South Korea is intelligence personnel, who is involved in military planning, and who is communicating with the United States. They know whom to target.
FILE - In this Sept. 19, 2017, photo, U.S. Army soldiers from the 2nd Infantry Division';s 2nd Armored Brigade Combat Team move during a joint military exercise between the U.S. and South Korea in Pocheon, South Korea. A South Korean lawmaker said Oct. 10, 2017, that North Korean hackers may have stolen highly classified military documents that include U.S.-South Korean wartime 'decapitation strike' plans against the North, according to South Korean media reports.
VOA: Are you saying North Korea hacked this plan?
Geers: It is entirely possible these plans were hacked and stolen. And it is possible that North Korea got help from Russia or China because their geopolitical interests align with North Korea's on occasion. Challenging the geopolitical interests and the United States, or just testing the cyberwar defenses and capabilities, is also a possibility. There is only one internet and cyberspace, and we are all in it. That is what has allowed North Korean attacks, even attacks on the White House, denial of service attacks.
VOA: Is it easy to hack this kind of classified documents?
Geers: This case, it could be that these plans might be in possession to 500 to 1,000 people, potentially. Unless it is really tightly held secret, it is hard to hang on to it. We have seen in the past that even the NSA and the CIA get hacked and information released in WikiLeaks. Supersecret three-letter agencies can be hacked. It might not be directly through internet.
VOA: Why does North Korea hack systems?
Geers: North Korea, they are under sanctions, they have a budget shortfall like every other government, so they might use cyberattacks to steal money, because money, as is everything is now, has been digitized. So it might purely be to gain money in a country that is actually very poor with nuclear weapons. That is one possibility. But number two, they really do want to know if they are about to be attacked hellip; they are going to want the plans. They need the classified military plans of foreign nations - in this case, the United States, Korea and Japan.
FILE - A student attends a white-hat hackers competition, co-hosted by the Defense Ministry and the National Intelligence Service, at the Korea Military Academy in Seoul, Sept. 29, 2013.
VOA: According to news reports, a major Russian telecommunications company has begun providing an internet connection to North Korea. What do you think about this?
Geers: I do think that Russia and China have geopolitical interests that may align with North Korea on occasion. There is always a collaboration hellip; like 'the enemy of my enemy is my friend' on occasion. That dynamic certainly could mean that Russia and China are involved in North Korea to a greater extent than we know. Russians would love to know the extent of U.S. capabilities in attacking what is called a hard target. So do the Chinese. It could very well be possible that they have personnel in North Korea that are studying our moves.
VOA: Are you suggesting that Russia, China and North Korea are aligned with each other in the battlefield of cyberwar, just like they were in the Cold War?
Geers: That's right. There's going to be a cooperation going on between allies. To some degree, traditional allies, they are going to have to work together in cyberspace. I think countries with an interest in supporting North Korea, even if it is only to slow down - let's say, in their perspective - the U.S. hegemony, or superpower status within Asia or within Europe. In other words, China or Russia, they might well align with Iran or North Korea on cyberissues as well as on a wide range of other issues.
VOA: Do you think there is a chance for North Korea to win a cyberwar with the U.S., South Korea or any other Western countries?
Geers: No. I think that North Korea would be a fairly easy target because it has fewer nodes, is easier to surveil, deny service or manipulate eventually. North Korea's threat would be pounding artillery, trying to fire missiles to Tokyo or the U.S. Now, if they have the nuclear bomb, that's threatening as well. But I think in the cyber perspective, they would go down quickly.
VOA: Where would a cyberwar be fought?
Geers: Cyberwar genuinely takes place all the time, even in peacetime. It involves espionage, and the modification of systems that will facilitate denial of service or scrambling of data that would lead to confusion or fear, uncertainties, doubts, or [the] inability to have a situational awareness over the battlespace during a real conflict.
VOA: Some argue that North Korea's high failure rate for missile launches might be due to the U.S. or other countries' cyberattacks. Is this possible?
Geers: Cyber basically is the key to everything today, because any kind of advanced weaponry will use information technology not only to scan the battlefield and understand where targets are, but also to defend themselves from inbound attacks as well. In the case of missiles, you might block critical information that they need in order to fly in the right direction. You can scramble information, too. You can get into computers and scramble the data. You can actually tell the missiles to fire in the wrong direction, or launch an attack on an adversary's own city.
An employee of the Korean Broadcasting System (KBS) transports computers on a trolley at KBS';s main building in Seoul, March 21, 2013. A hacking attack that brought down three South Korean broadcasters and two major commercial banks was identified by most commentators as Pyongyang flexing its muscles as military tensions on the divided peninsula skyrocket.
VOA: So you can change the missile target points by manipulating the data?
Geers: Yes. This is possible because [the computer] is just doing what it is told. Applications or the processing power of the computer and the industrial control systems around it are simply following orders, going to latitude and longitude points on the Earth. In theory, if foreign actors could get inside that information loop, they can change the target, and the computer might have no way of knowing whether that is the right or wrong target. Computers just respond to commands. In that way, they can be very smart and very stupid at the same time.
VOA: So you are saying the U.S. or other countries can interfere with North Korea's missile system?
Geers: Yes. Western countries - in this case, South Korea, the U.S. or Japan - in fact, they would be fools not to have a wide range of options addressing North Korean missile threats. Some of them look traditional and some of them are probably quite experimental. And even China [can do this], because China may have some interests in keeping the North Korean threat below a certain threshold.
VOA: Are there instances where a cyberattack has been used in a military operation?
Geers: [Israel bombed] a nuclear reactor in Iraq in [1981] and Syria in 2007. They have threatened to do it today in Iran, but it is very unclear if it might work. But in the two previous cases, it was the surprise attack model, in which planes flew under the radar into Iraq. In 2007, it is not known, but it is assumed by analysts, that a cyberattack played a role in turning off Syrian air defenses so that Israeli planes could fly into Syria and destroy the target without being seen. The Middle East provides good analogy for the Korean Peninsula because war could start quickly in either place.
The Stuxnet attack was a Western attack on the Iranian nuclear weapons program. It illustrates the amazing degree of power of a cyberattack. You are telling a system to destroy itself physically, because this is an industrial system, but controlled basically by computers operating Windows and the applications that manage it. So in an aggressive attack scenario, you can change code so that machine would destroy itself, and yet code is also telling the human manager of the system that everything is OK.
This report originated on VOA's Korean service. Share
Share
 Tweet
Tweet
 Share
Share
 Flip
Flip
 Email
Email
Watch latest videos
Subscribe and Follow
Get a daily dose of North Korea Times news through our daily email, its complimentary and keeps you fully up to date with world and business news as well.
News RELEASES
Publish news of your business, community or sports group, personnel appointments, major event and more by submitting a news release to North Korea Times.
More InformationInternational
SectionNew U.S. guidelines may cut daily alcohol limit from advice
WASHINGTON, D.C.: The U.S. government is preparing to revise its influential dietary advice, with a significant shift: dropping the...
UBS: Over 379,000 Americans became millionaires last year
ZURICH, Switzerland: The U.S. saw an extraordinary rise in wealth last year, with more than 1,000 people crossing into millionaire...
The Hague faces lockdown for global leaders' meet
THE HAGUE, Netherlands: The city that prides itself on being a beacon of peace and justice—home to institutions like the International...
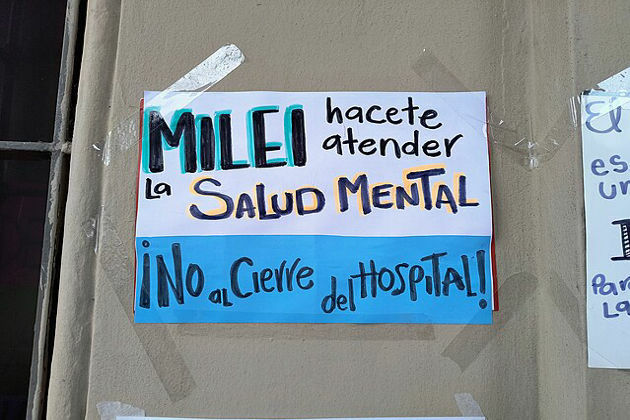
Drug shortages and layoffs spark health crisis in Argentina
BUENOS AIRES, Argentina: Since taking office in December 2023, Argentine President Javier Milei has implemented sweeping austerity...
Volcanic ash grounds flights to Indonesia, disrupts travel to Bali
LEMBATA, Indonesia: Indonesia's Mount Lewotobi Laki Laki erupted dramatically on June 18, generating substantial ash and smoke plumes....
REE misjudgment caused April blackout, says Spain's energy chief
MADRID, Spain: A routine oversight by Spain's power grid operator, REE, has been identified as the trigger behind the large-scale blackout...
Business
SectionAmazon’s Zoox unveils plan to build 10,000 robotaxis a year
HAYWARD, California: In a significant step toward its commercial debut, Amazon-owned Zoox has unveiled its first factory dedicated...
Brazil aims to restart poultry trade after bird flu clearance
SAO PAULO, Brazil: Brazil is taking confident steps to restore its dominance in global poultry exports after declaring its commercial...
U.S. stocks restricted by tensions in Middle East
NEW YORK, New YorK - U.S. stocks closed mixed on Friday, with gains and losses modest, as investors and traders weighed up the escalation...
US consumers cut back after early surge ahead of Trump tariffs
WASHINGTON, D.C.: Retail sales dropped sharply in May as consumer spending slowed after a strong start to the year, primarily due to...
Mitsubishi joins automakers raising prices after import tariffs
WASHINGTON, D.C.: Mitsubishi Motors is the latest automaker to raise prices in the United States, joining a growing list of car companies...
Lilly makes $1.3 billion move to expand into gene-edited heart drugs
INDIANAPOLIS, Indiana: Eli Lilly is making a bold play in cardiovascular gene therapy, announcing plans to acquire its partner Verve...